Significant increases seen in software engineering enrollments
Tag: SYSTEM SECURITY/HACKERS
Securing the internet
SMU Office of Research & Tech Transfer – While many people can name an Internet Service Provider (ISP) and describe what an ISP does, fewer people know the exchange of internet traffic that happens between different ISPs’ networks, which are…
New technique to prevent imaging cyberthreats proposed by Ben-Gurion University researchers
Paper to be presented during the International Conference on Artificial Intelligence in Medicine (AIME 2020)
Journalists invited to cover the Virtual HLF this September 21-25
Traverse separation with a diverse online scientific program
What is artificial intelligence?
A conversation between an AI engineer and a humanities researcher
Researchers got busy: After nearly allowing the solution to a math riddle
Researchers thought that they were five years away from solving a math riddle from the 1980’s. In reality, and without knowing, they had nearly cracked the problem and had jus
Security gap allows eavesdropping on mobile phone calls
Calls via the LTE mobile network, also known as 4G, are encrypted and should therefore be tap-proof. However, researchers from the Horst Görtz Institute for IT Security (HGI) at Ruhr-Universität Bochum have shown that this is not always the case.…
Piotr Roztocki wins 2020 Paul Baran Young Scholar Award for his innovative work
First Canadian to be recognized by the Marconi Society’s Award in quantum photonic
Consumers don’t fully trust smart home technologies
Smart home technologies are marketed to enhance your home and make life easier. However, UK consumers are not convinced that they can trust the privacy and security of these technologies, a study by WMG, University of Warwick has shown.Smart Home…
New method to defend against smart home cyber attacks developed by Ben-Gurion University researchers
BEER-SHEVA, Israel…August 3, 2020 – Instead of relying on customers to protect their vulnerable smart home devices from being used in cyberattacks, Ben-Gurion University of the Negev (BGU) and National University of Singapore (NUS) researchers have developed a new method…
Software of autonomous driving systems
TU Graz develops methods for the generation of simulation scenarios and internal error regulation
NIST’s post-quantum cryptography program enters ‘selection round’
Chosen algorithms will become part of first standard devised to counter quantum decryption threat.

No honor among cyber thieves
A backstabbing crime boss and thousands of people looking for free tutorials on hacking and identity theft were two of the more interesting findings of a study examining user activity on two online “carding forums,” illegal sites that specialize in stolen credit card information.
No honor among cyber thieves
A backstabbing crime boss and thousands of people looking for free tutorials on hacking and identity theft were two of the more interesting findings of a study examining user activity on two online “carding forums,” illegal sites that specialize in…
Cyber expert on ‘insider threat’ attacks
Dr Duncan Hodges, Senior Lecturer in Cyberspace Operations, Cranfield University, is actively researching insider threats such as the recent Twitter attacck . He and researcher Katie Paxton-Fear are presenting this paper Understanding Insider Threat Attacks Using Natural Language Processing , at the HCI International Conference…
New research reveals privacy risks of home security cameras
An international study has used data from a major home Internet Protocol (IP) security camera provider to evaluate potential privacy risks for users.
Expanding access to cyber research tools
ALBUQUERQUE, N.M. — Faculty and students at Purdue University now have access to cybersecurity research software developed at Sandia National Laboratories. This marks the first time Sandia has collaborated with an academic community to make its cyber software widely available.…
TU Darmstadt: Pause button for light particles
Researchers at TU Darmstadt halt individual photons
TU Darmstadt: Pause button for light particles
Researchers at TU Darmstadt halt individual photons
National effort joins forces to build a secure smart home
Research focuses on strengthening trust around the household ‘Internet of Things’
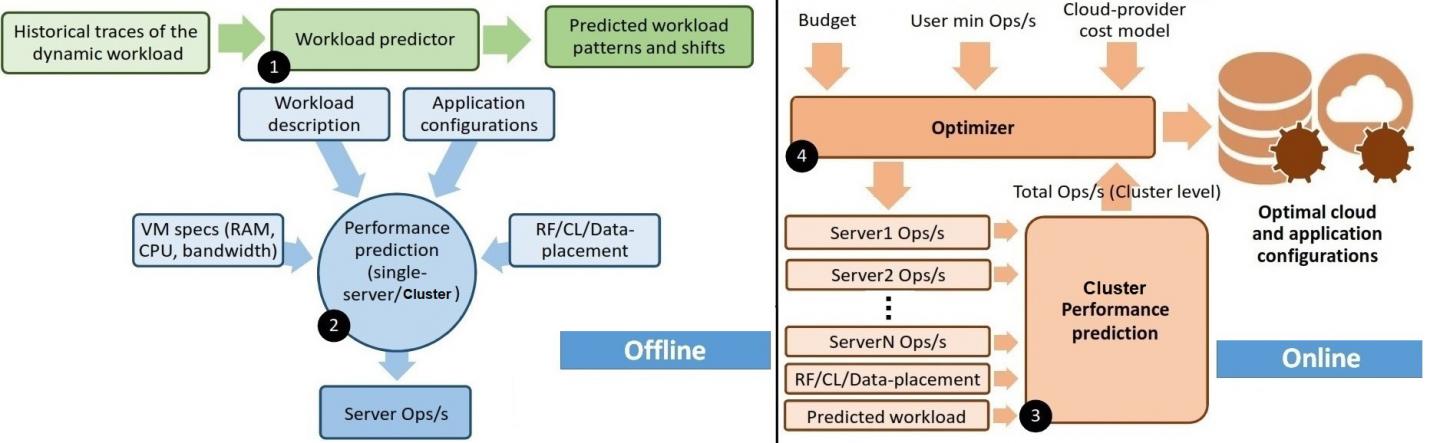
Technology for cloud efficiency for databases during data-intensive COVID-19 pandemic
A Purdue University data science and machine learning innovator wants to help organizations and users get the most for their money when it comes to cloud-based databases.
Technology for cloud efficiency for databases during data-intensive COVID-19 pandemic
WEST LAFAYETTE, Ind. – A Purdue University data science and machine learning innovator wants to help organizations and users get the most for their money when it comes to cloud-based databases. Her same technology may help self-driving vehicles operate more…
Keeping water and energy secure
Engineering researcher studies smart city cybersecurity
Technology for cloud efficiency for databases during data-intensive COVID-19 pandemic
WEST LAFAYETTE, Ind. – A Purdue University data science and machine learning innovator wants to help organizations and users get the most for their money when it comes to cloud-based databases. Her same technology may help self-driving vehicles operate more…
Keeping water and energy secure
Engineering researcher studies smart city cybersecurity
Pioneer of modern datacenter design receives Eckert-Mauchly Award
Google’s Luiz Barroso recognized as visionary architect of warehouse-scale computing
Pioneer of modern datacenter design receives Eckert-Mauchly Award
Google’s Luiz Barroso recognized as visionary architect of warehouse-scale computing
Army scientist receives top honors for pioneering big data security
RESEARCH TRIANGLE PARK, N.C. — An Army scientist earned top honors from IEEE for big data security and privacy research. IEEE is the world’s largest technical professional organization dedicated to advancing technology for the benefit of humanity. Dr. Cliff Wang,…
Tel Aviv University and IDC Herzliya researchers thwart large-scale cyberattack threat
Attack could have been 800 times more destructive than the cyberattack that brought down parts of the Internet on the US’s East Coast in 2016
Army scientist receives top honors for pioneering big data security
RESEARCH TRIANGLE PARK, N.C. — An Army scientist earned top honors from IEEE for big data security and privacy research. IEEE is the world’s largest technical professional organization dedicated to advancing technology for the benefit of humanity. Dr. Cliff Wang,…
Tel Aviv University and IDC Herzliya researchers thwart large-scale cyberattack threat
Attack could have been 800 times more destructive than the cyberattack that brought down parts of the Internet on the US’s East Coast in 2016
Privacy flaws in security and doorbell cameras discovered by Florida Tech Student
Ring, Nest, SimpliSafe and other manufacturers plan fixes
Privacy flaws in security and doorbell cameras discovered by Florida Tech Student
Ring, Nest, SimpliSafe and other manufacturers plan fixes
Observations of robotic swarm behavior can help workers safely navigate disaster sites
Using biologically inspired robotic swarms consisting of large groups of robots that have been programmed to operate cooperatively, much like individuals in an ant or bee colony, scientists from the University of Colorado demonstrate that the locally observed distribution of…
Genetic barcodes can ensure authentic DNA fingerprints
Researchers propose a way of ensuring that genetic samples taken in the field for DNA fingerprinting arrive at the laboratory unaltered
Genetic barcodes can ensure authentic DNA fingerprints
Researchers propose a way of ensuring that genetic samples taken in the field for DNA fingerprinting arrive at the laboratory unaltered
ACM honors computing innovators for advances in research, education and industry
Contributions recognized in areas including the internet, algorithms and artificial intelligence
New award for the article ‘An analysis of the Pre-installed Android Software’
The IEEE S&P conference has bestowed the Best Practical Paper Award to Julien Gamba, Mohammed Rashed, Abbas Razaghpanah, Juan Tapiador and Narseo Vallina-Rodriguez for this work
ACM honors computing innovators for advances in research, education and industry
Contributions recognized in areas including the internet, algorithms and artificial intelligence
New award for the article ‘An analysis of the Pre-installed Android Software’
The IEEE S&P conference has bestowed the Best Practical Paper Award to Julien Gamba, Mohammed Rashed, Abbas Razaghpanah, Juan Tapiador and Narseo Vallina-Rodriguez for this work
Leading European computing society releases statement on COVID contact tracing
Group calls for transparency, interoperability, privacy, and scrutiny
Leading European computing society releases statement on COVID contact tracing
Group calls for transparency, interoperability, privacy, and scrutiny
We believe we’re less likely than others are to fall for online scams
New cybersecurity study has significant implications as we increasingly work remotely during COVID-19 pandemic
We believe we’re less likely than others are to fall for online scams
New cybersecurity study has significant implications as we increasingly work remotely during COVID-19 pandemic
New Home Office funded report urges greater action for cybercrime victims
The first major UK study into victims of computer misuse crime has exposed the serious harm some victim’s experience, as well as barriers to reporting such offences, receiving support, achieving justice and the precarious resources dedicated by the police to…
New Home Office funded report urges greater action for cybercrime victims
The first major UK study into victims of computer misuse crime has exposed the serious harm some victim’s experience, as well as barriers to reporting such offences, receiving support, achieving justice and the precarious resources dedicated by the police to…
Novel research speeds up threat detection, prevention for Army missions
Threat detection and prevention are essential to ensuring the safety and security of warfighters. Researchers have developed a way to speed up the processing of extremely large graphs and data, making the most efficient use of modern Army computational resources…
Novel research speeds up threat detection, prevention for Army missions
Threat detection and prevention are essential to ensuring the safety and security of warfighters. Researchers have developed a way to speed up the processing of extremely large graphs and data, making the most efficient use of modern Army computational resources…
EPFL researchers put proximity tracing app to the test
Over the past two weeks, EPFL computer scientists have been testing and refining the smartphone-based system developed by the international Decentralized Privacy-Preserving Proximity Tracing project (DP3T), with the help of the Swiss Army. Their goal: to optimize the app’s ability…
The law of Facebook: Borders, regulation and global social media
Borders, regulation and global social media